Security aligned IT Support services speak out on the current appalling levels of awareness
There is never a safety level enough to relax and watch the data of any organization grow. Passwords used to be sufficient, not they are child’s play to hackers, what should we be looking at for security, Cloud Tweak security experts spoke out.
DESPITE RECORD BREACHES, SECURE THIRD PARTY ACCESS STILL NOT AN IT PRIORITY!
Research has revealed that third parties directly cause 63 percent of all data breaches. From HVAC contractors, to trusted IT solutions baltimore, to supply chain analysts and beyond, the threats posed by third parties are real and growing. Deloitte, in its Global Survey 2016 of third party risk, reported that 87 percent of respondents had faced a disruptive incident with third parties in the last two to three years…Read more here
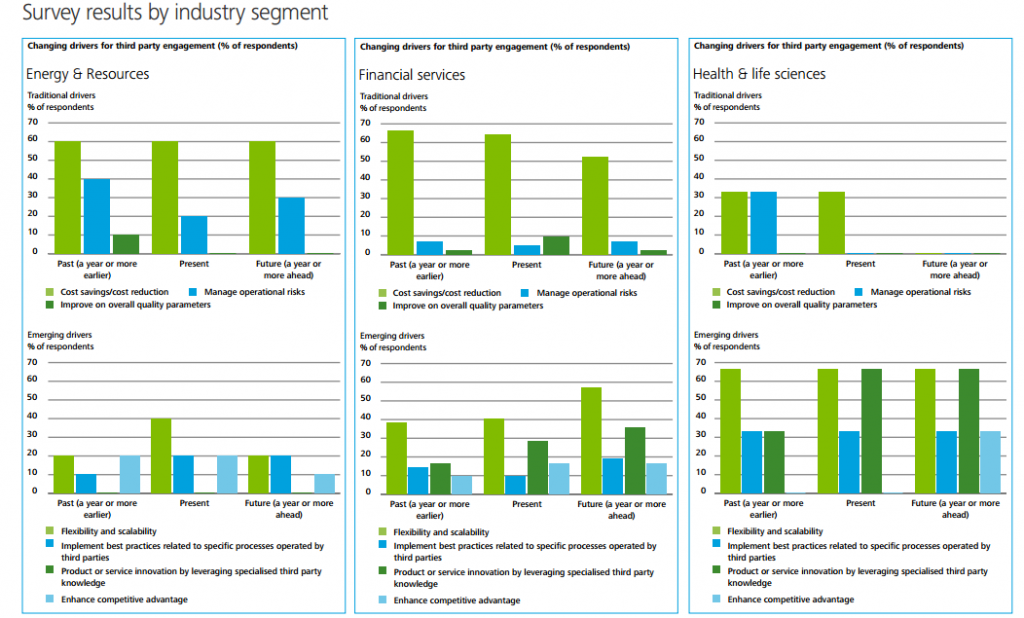
Findings of 3rd party related breaches in 2016 so far. Image credit: Cloud Tweaks.
Perhaps the most appalling of facts is that we still look to the least experienced personnel in our companies to manage security.
Cartoon credit: John Klossnet
As the year progresses, more companies will migrate to the cloud, and with the shift we will lose a lot in terms of security. Some of the security challenges are hinted by the video below:
Video: Youtube
Cloud, SDN, And Security Complications
As enterprises migrate to the cloud and SDN, they face challenges in maintaining security…
…It’s true that more organizations are making investments in cloud, software-defined networking, and virtualization, and that’s a good thing in the long run. These investments will help companies realize new efficiencies, increased agility and significant cost savings. But at the moment, we’re still in the transition phase of the software-based movement.
While more and more applications are moving to the cloud, businesses are still relying on their on-premises infrastructure for many critical functions and applications. That’s not going away anytime soon. The result of this mid-point in migration is greater network complexity. IT teams must maintain security policies and practices for both on-premises physical and cloud-based environments.
There are three key challenges to managing the complex enterprise network as we move through the cloud/SDN transition phase:
- Cloud know-how. The skillsets required to effectively manage traditional on-premises infrastructure and cloud-based infrastructure are vastly different.
- Increased attack surface. The proliferation of cloud platforms and technologies, coupled with the explosion of connected mobile devices, means that the attack surface of the network is larger than ever.
- Confusion over technology investments. There are solutions available today to help IT pros manage, secure and optimize their heterogeneous networks, even in the face of a workforce shortages.
There are others still optimistic that we can win the security war, hoping for more companies to take heed and change their systems accordingly. Many of them offer sound advice through the Dark Reading platform.
How Secure is Secure? Tips For Investing In The Right Strategy
Business alignment, defense-in-depth and a phased approach are three principles to follow when building out a solid security program.
Information is an asset; it’s the lifeblood of businesses. Companies know this — and so do criminals. That’s why it’s more important than ever for security professionals to think more expansively about information as an asset, compliance controls, privacy, and transparency and to take a proactive approach to security, beginning with a strong security strategy.
In order to define your security strategy, you first need to determine the right security investment for your organization. There are three criteria that can help: see criteria here